Breaking News
Postgresql Ssl Client Certificate
суббота 28 марта admin 58
In this situation I tend to pull out Wireshark and snoop the SSL negotiation to make sure the client certificate is really being offered by the client. I suggest using. Establish Secure SSL Connection to PostgreSQL Database Server PostgreSQL Server Configuration. Within the instruction below. Client Certificates. Now, let’s create one more set of SSL certificate files for client instance. Establish Connection via PgAdmin. Eventually, after server and client.
PostgreSQL has native support for using SSL connections to encrypt client/server communications for increased security. This requires that OpenSSL is installed on both client and server systems and that support in PostgreSQL is enabled at build time (see Chapter 15).
With SSL support compiled in, the PostgreSQL server can be started with SSL enabled by setting the parameter ssl to on in postgresql.conf. The server will listen for both normal and SSL connections on the same TCP port, and will negotiate with any connecting client on whether to use SSL. By default, this is at the client's option; see Section 19.1 about how to set up the server to require use of SSL for some or all connections.
PostgreSQL reads the system-wide OpenSSL configuration file. By default, this file is named openssl.cnf and is located in the directory reported by openssl version -d. This default can be overridden by setting environment variable OPENSSL_CONF to the name of the desired configuration file.
OpenSSL supports a wide range of ciphers and authentication algorithms, of varying strength. While a list of ciphers can be specified in the OpenSSL configuration file, you can specify ciphers specifically for use by the database server by modifying ssl_ciphers in postgresql.conf.
Note: It is possible to have authentication without encryption overhead by using NULL-SHA or NULL-MD5 ciphers. However, a man-in-the-middle could read and pass communications between client and server. Also, encryption overhead is minimal compared to the overhead of authentication. For these reasons NULL ciphers are not recommended.
To start in SSL mode, the files server.crt and server.key must exist in the server's data directory. These files should contain the server certificate and private key, respectively. On Unix systems, the permissions on server.key must disallow any access to world or group; achieve this by the command chmod 0600 server.key. If the private key is protected with a passphrase, the server will prompt for the passphrase and will not start until it has been entered.
In some cases, the server certificate might be signed by an 'intermediate' certificate authority, rather than one that is directly trusted by clients. To use such a certificate, append the certificate of the signing authority to the server.crt file, then its parent authority's certificate, and so on up to a 'root' authority that is trusted by the clients. The root certificate should be included in every case where server.crt contains more than one certificate.
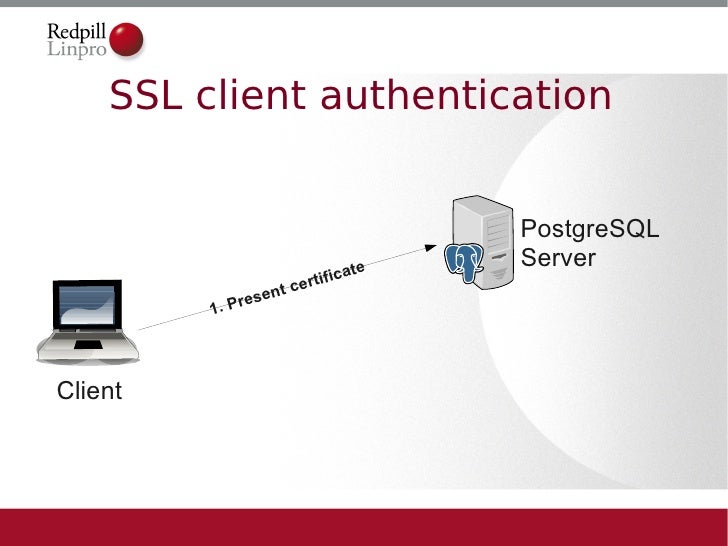
17.9.1. Using Client Certificates
To require the client to supply a trusted certificate, place certificates of the certificate authorities (CAs) you trust in the file root.crt in the data directory, and set the clientcert parameter to 1 on the appropriate hostssl line(s) in pg_hba.conf. A certificate will then be requested from the client during SSL connection startup. (See Section 31.17 for a description of how to set up certificates on the client.) The server will verify that the client's certificate is signed by one of the trusted certificate authorities. Certificate Revocation List (CRL) entries are also checked if the file root.crl exists. (See http://h71000.www7.hp.com/doc/83final/ba554_90007/ch04s02.html for diagrams showing SSL certificate usage.)
The clientcert option in pg_hba.conf is available for all authentication methods, but only for rows specified as hostssl. When clientcert is not specified or is set to 0, the server will still verify presented client certificates against root.crt if that file exists — but it will not insist that a client certificate be presented.
Note that root.crt lists the top-level CAs that are considered trusted for signing client certificates. In principle it need not list the CA that signed the server's certificate, though in most cases that CA would also be trusted for client certificates.
If you are setting up client certificates, you may wish to use the cert authentication method, so that the certificates control user authentication as well as providing connection security. See Section 19.3.10 for details.
17.9.2. SSL Server File Usage
Table 17-3 summarizes the files that are relevant to the SSL setup on the server.
Table 17-3. SSL Server File Usage
| File | Contents | Effect |
|---|---|---|
| $PGDATA/server.crt | server certificate | sent to client to indicate server's identity |
| $PGDATA/server.key | server private key | proves server certificate was sent by the owner; does not indicate certificate owner is trustworthy |
| $PGDATA/root.crt | trusted certificate authorities | checks that client certificate is signed by a trusted certificate authority |
| $PGDATA/root.crl | certificates revoked by certificate authorities | client certificate must not be on this list |
The files server.key, server.crt, root.crt, and root.crl are only examined during server start; so you must restart the server for changes in them to take effect.
17.9.3. Creating a Self-signed Certificate
To create a quick self-signed certificate for the server, use the following OpenSSL command:
Fill out the information that openssl asks for. Make sure you enter the local host name as 'Common Name'; the challenge password can be left blank. The program will generate a key that is passphrase protected; it will not accept a passphrase that is less than four characters long. To remove the passphrase (as you must if you want automatic start-up of the server), run the commands:
Enter the old passphrase to unlock the existing key. Now do:
to turn the certificate into a self-signed certificate and to copy the key and certificate to where the server will look for them. Finally do:
because the server will reject the file if its permissions are more liberal than this. For more details on how to create your server private key and certificate, refer to the OpenSSL documentation.
A self-signed certificate can be used for testing, but a certificate signed by a certificate authority (CA) (either one of the global CAs or a local one) should be used in production so that clients can verify the server's identity. If all the clients are local to the organization, using a local CA is recommended.
PostgreSQL has native support for using SSL connections to encrypt client/server communications for increased security. See Section 17.8 for details about the server-side SSL functionality.
libpq reads the system-wide OpenSSL configuration file. By default, this file is named openssl.cnf and is located in the directory reported by openssl version -d. This default can be overridden by setting environment variable OPENSSL_CONF to the name of the desired configuration file.
30.17.1. Certificate verification
By default, PostgreSQL will not perform any verification of the server certificate. This means that it is possible to spoof the server identity (for example by modifying a DNS record or by taking over the server IP address) without the client knowing. In order to prevent this, SSL certificate verification must be used.
Gamers choose from one of 16 species and battle it out for galactic domination on 800 planets using a point-and-click interface. Pax imperia eminent domain no cd patch. A sequel to the popular Mac game, Pax Imperia: Eminent Domain serves up a sturdy helping of hardcore space strategy and resource-management gameplay.
If the parameter sslmode is set to verify-ca libpq will verify that the server is trustworthy by checking the certificate chain up to a trusted CA. If sslmode is set to verify-full, libpq will also verify that the server hostname matches that of the certificate. The SSL connection will fail if the server certificate cannot be verified. verify-full is recommended in most security sensitive environments.
In verify-full mode, the cn attribute of the certificate is matched against the hostname. If the cn attribute starts with an asterisk (*), it will be treated as a wildcard, and will match all characters except a dot (.). This means the certificate will not match subdomains. If the connection is made using an IP address instead of a hostname, the IP address will be matched (without doing any DNS lookups).
To allow verification, the certificate of a trusted CA must be placed in the file ~/.postgresql/root.crt in the user's home directory. (On Microsoft Windows the file is named %APPDATA%postgresqlroot.crt.)
Certificate Revocation List (CRL) entries are also checked if the file ~/.postgresql/root.crl exists (%APPDATA%postgresqlroot.crl on Microsoft Windows).
The location of the root certificate store and the CRL can be overridden by the connection parameters sslrootcert and sslcrl or the environment variables PGSSLROOTCERT and PGSSLCRL.
Note: For backwards compatibility with earlier versions of PostgreSQL, if a root CA file exists, the behavior of sslmode=require will be the same as that of verify-ca, meaning the sever certificate is validated against the CA. Relying on this behavior is discouraged, and applications that need certificate validation should always use verify-ca or verify-full.
30.17.2. Client certificates
If the server requests a trusted client certificate, libpq will send the certificate stored in file ~/.postgresql/postgresql.crt in the user's home directory. The certificate must be signed by one of the certificate authorities (CA) trusted by the server. A matching private key file ~/.postgresql/postgresql.key must also be present. The private key file must not allow any access to world or group; achieve this by the command chmod 0600 ~/.postgresql/postgresql.key. On Microsoft Windows these files are named %APPDATA%postgresqlpostgresql.crt and %APPDATA%postgresqlpostgresql.key, and there is no special permissions check since the directory is presumed secure. The location of the certificate and key files can be overridden by the connection parameters sslcert and sslkey or the environment variables PGSSLCERT and PGSSLKEY.
30.17.3. Protection provided in different modes
The different values for the sslmode parameter provide different levels of protection, in different environments. SSL itself provides protection against three different types of attacks:
Table 30-2. SSL attacks
| Type | Description |
|---|---|
| Eavesdropping | If a third party can listen to the network traffic between the client and the server, it can read both connection information (including the username and password) and the data that is passed. SSL uses encryption to prevent this. |
| Man in the middle (MITM) | If a third party can modify the data while passing between the client and server, it can pretend to be the server and therefore see and modify data even if it is encrypted. The third party can then forward the connection information and data to the original server, making it impossible to detect this attack. Common vectors to do this include DNS poisoning and address hijacking, whereby the client is directed to a different server than intended. There are also several other attack methods that can accomplish this. SSL uses certificate verification to prevent this, by authenticating the server to the client. |
| Impersonation | If a third party can pretend to be an authorized client, it can simply access data it should not have access to. Typically this can happen through insecure password management. SSL uses client certificates to prevent this, by making sure that only holders of valid certificates can access the server. |
For a connection to be known secure, the two first of these have to be set up on both the client and the server before the connection is made. If it is only configured on the server, the client may end up sending sensitive information (e.g. passwords) before it knows that the server requires high security. In libpq, this is controlled by setting the sslmode parameter to verify-full or verify-ca, and providing the system with a root certificate to verify against. This is analogous to using a httpsURL for encrypted web browsing.
Once the server has been authenticated, the client can pass sensitive data. This means that up until this point, the client does not need to know if certificates will be used for authentication, making it safe to specify this only in the server configuration.
All SSL options carry overhead in the form of encryption and key-exchange, and it is a tradeoff that has to be made between performance and security. The following table illustrates the risks the different sslmode values protect against, and what statement they make about security and overhead:
Table 30-3. SSL mode descriptions
| sslmode | Eavesdropping protection | MITM protection | Statement |
|---|---|---|---|
| disable | No | No | I don't care about security, and I don't want to pay the overhead of encryption. |
| allow | Maybe | No | I don't care about security, but I will pay the overhead of encryption if the server insists on it. |
| prefer | Maybe | No | I don't care about encryption, but I wish to pay the overhead of encryption if the server supports it. |
| require | Yes | No | I want my data to be encrypted, and I accept the overhead. I trust that the network will make sure I always connect to the server I want. |
| verify-ca | Yes | Depends on CA-policy | I want my data encrypted, and I accept the overhead. I want to be sure that I connect to a server that I trust. |
| verify-full | Yes | Yes | I want my data encrypted, and I accept the overhead. I want to be sure that I connect to a server I trust, and that it's the one I specify. |
The difference between verify-ca and verify-full depends on the policy of the root CA. If a public CA is used, verify-ca allows connections to a server that somebody else may have registered with the CA to succeed. In this case, verify-full should always be used. If a local CA is used, or even a self-signed certificate, using verify-ca often provides enough protection.
The default value for sslmode is prefer. As is shown in the table, this makes no sense from a security point of view, and it only promises performance overhead if possible. It is only provided as the default for backwards compatibility, and not recommended in secure deployments.
30.17.4. SSL File Usage
Table 30-4. Libpq/Client SSL File Usage
| File | Contents | Effect |
|---|---|---|
| ~/.postgresql/postgresql.crt | client certificate | requested by server |
| ~/.postgresql/postgresql.key | client private key | proves client certificate sent by owner; does not indicate certificate owner is trustworthy |
| ~/.postgresql/root.crt | trusted certificate authorities | checks server certificate is signed by a trusted certificate authority |
| ~/.postgresql/root.crl | certificates revoked by certificate authorities | server certificate must not be on this list |
30.17.5. SSL library initialization
If your application initializes libssl and/or libcrypto libraries and libpq is built with SSL support, you should call PQinitOpenSSL to tell libpq that the libssl and/or libcrypto libraries have been initialized by your application, so that libpq will not also initialize those libraries. See http://h71000.www7.hp.com/doc/83final/BA554_90007/ch04.html for details on the SSL API.
PQinitOpenSSLAllows applications to select which security libraries to initialize.
When do_ssl is non-zero, libpq will initialize the OpenSSL library before first opening a database connection. When do_crypto is non-zero, the libcrypto library will be initialized. By default (if PQinitOpenSSL is not called), both libraries are initialized. When SSL support is not compiled in, this function is present but does nothing.
If your application uses and initializes either OpenSSL or its underlying libcrypto library, you must call this function with zeroes for the appropriate parameter(s) before first opening a database connection. Also be sure that you have done that initialization before opening a database connection.
PQinitSSLAllows applications to select which security libraries to initialize.
Childish Gambino’s tracksbypublished on 2020-03-21T15:52:45Zbypublished on 2020-03-21T07:14:15Zbypublished on 2020-03-21T07:14:12Zbypublished on 2020-03-21T07:14:08Zbypublished on 2020-03-21T07:14:07Zbypublished on 2020-03-21T07:14:06Zbypublished on 2020-03-21T07:14:03Zbypublished on 2020-03-21T07:14:01Zbypublished on 2020-03-21T07:14:00Zbypublished on 2020-03-21T07:13:59Zbypublished on 2020-03-21T07:13:59Zbypublished on 2020-03-21T07:13:57Zbypublished on 2020-03-21T07:13:55Z. Because of the internet download childish gambino.
This function is equivalent to PQinitOpenSSL(do_ssl, do_ssl). It is sufficient for applications that initialize both or neither of OpenSSL and libcrypto.
PQinitSSL has been present since PostgreSQL 8.0, while PQinitOpenSSL was added in PostgreSQL 8.4, so PQinitSSL might be preferable for applications that need to work with older versions of libpq.